Background
jLogo Programming
- Commanding a Turtle
- Pseudocode
- Adding New Commands
- Iteration & Animation
- Hierarchical Structure
- Procedure Inputs
- Primitive Operators
- Defining Operators
- Words & Sentences
- User Interface Events
- What If? (Predicates)
- Recursion
- Local Variables
- Global Variables
- Word/Sentence Iteration
- Mastermind Project
- Turtles As Actors
- Arrays
- File Input/Output
Java
- A Java Program
- What's a Class?
- Extending Existing Classes
- Types
- Turtle Graphics
- Control Flow
- User Interface Events
Appendices
Updates
Lastly
Thinking About [TLC] Logo - Procedure Inputs
|
Procedure Inputs
from Thinking About [TLC] Logo, |
|
But a box is a box regardless of the length of its sides. We want to define one message named box that allows us to say what the length of each side should be.
When we define a message that will require more than just its name when we use it, we need some way to indicate that additional information must be provided with the message. Also, we need to indicate how that additional information is to be used in the definition.
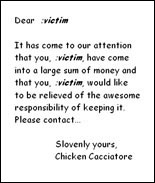
The problem we face is like that of creating a form letter that leaves spaces for the name of the victim. When it comes time to send a message we fill in all the appropriate places. For example,
Dear :victim
It has come to our attention that you, :victim, have
come into a large sum of money and that you, :victim,
would like to be relieved of the awesome responsibility
of keeping it. Please contact...
Slovenly yours,
Chicken Cacciatore
This is exactly what we need. Therefore we have called this the Junk Mail Model of Computation. In Junk Mail Computing we can embellish our simple to definitions with these dot-ified names. Thus a general, universal, and all-purpose box maker can be named box and defined as:
to box :side
repeat 4 [fd :side rt 90]
end
When it comes time to actually make a box of size 15, for example, we will write
box 15
and the right thing will happen.
That is, the turtle will find the name box in the message dictionary and will notice that it needs a value to substitute for the victim slot :side. Fortunately for us (and the turtle) we have supplied a number (15), for if nothing is provided to fill in the slot then the definition won't make sense to the turtle. And we don't want to mess with an angry turtle.
Before going on to more exciting turtle functions we should think a bit more about Junk Mail Computing (called JMC) and how our armored friend might perform the operations. So here it is, when the turtle retreats inside its shell after receiving the message
box 10
- It rummages through its list of known message indicators, looking for box.
- It finds that the box recipe is a form letter.
Since box :side is defined as repeat 4 [fd :side rt 90], it it substitutes 10 for :side and replaces the problem of box 10 with
repeat 4 [fd 10 rt 90]
It busily goes to work on this problem and in short order has flopped around the screen as expected.
This is all there is to Junk Mail Computing:
- The request is a message sequence that is "obvious" - like fd or rt 90. These are the primitive operations that the turtle is born with and they just get done; no fuss, no muss.
- The request uses a defined word. The beast looks up the word, sees if it requires some values for victims, and if so, either complains if they are not given, or substitutes them into the definition if they are given. The turtle then tries to satisfy the requests in the new sequence of messages. Each of these requests will, itself, be a case of 1 or 2.
